In order to connect to external SFTP, you might need a couple of private & public keys, instead of the less secure login+password alternative. Here’s how to create a new pair, without interaction
🔑🖥️🔒
Prerequisites
- UNIX basics (ls, cat, cd, ~)
- An SSH key is a text file, it can be read by any text editor
- There are 2 keys : a public one and a private one. So there are 2 files. It is a pair.
- A private key MUST NOT be shared by any mean. It is not meant to be shared.
- Only the public key has to be shared and can be shared via a non-encrypted way (i.e. via email)
- This method generates the key pair via the standard unix utility
ssh-keygen, ssh-keygen doc on wikipedia
Workflow
loadLibrary('fco:helpers');
var filename = '~/.ssh/id_rsa';
var cmd = 'ssh-keygen -t rsa -f '+filename+' -q -P ""';
//exec(cmd);
exec('ls '+filename+'*');
exec('cat '+filename+'.pub');
Leave l. 6 uncommented first, to check the existence of an already created key pair.
Uncomment to generate.
Log result:
fco:helpers | executing | ls ~/.ssh/id_rsa*
/usr/local/neolane/.ssh/id_rsa
/usr/local/neolane/.ssh/id_rsa.old
/usr/local/neolane/.ssh/id_rsa.pub
/usr/local/neolane/.ssh/id_rsa.pub.old
fco:helpers | executing | cat ~/.ssh/id_rsa.pub
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDFwPsIUf7FBgT0Bsh[...] root@instance-prod1
The public key is the last line, from “ssh-rsa” to “root@instance-prod1” (included).
Usage with the standard File Export SFTP activity
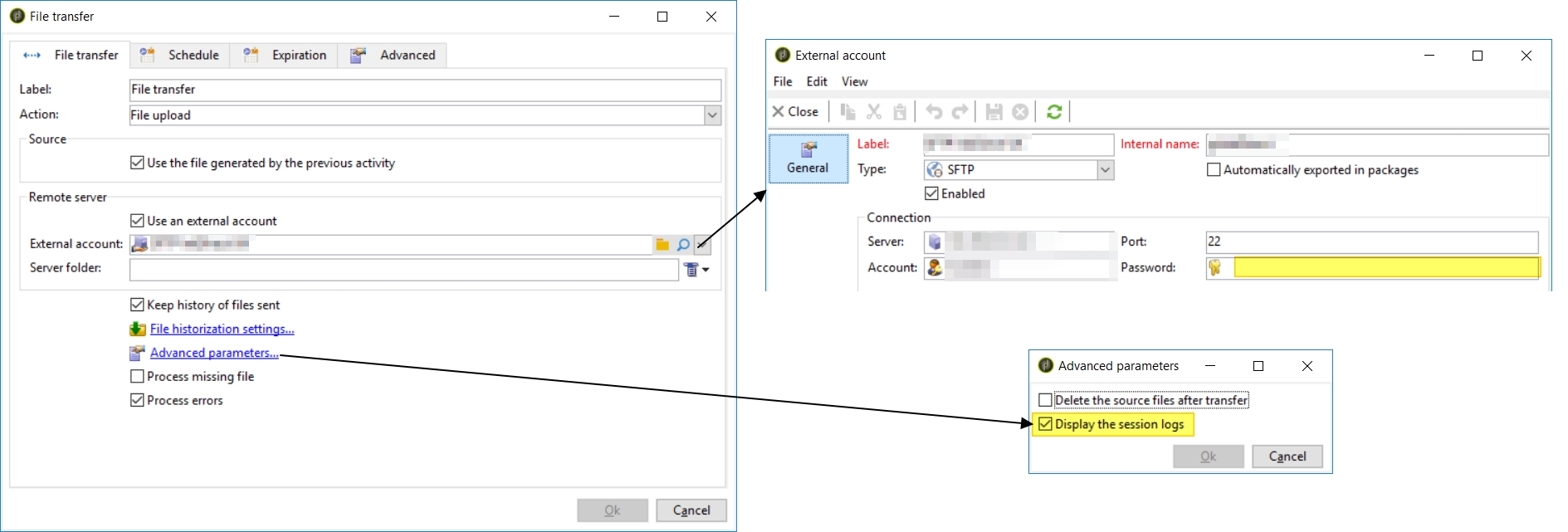
Create an external account of type SFTP, with a server (hostname), a port (default to 22) and an account (username). The password is empty, because the identification method is going to use the SSH key pair.
The SFTP activity is configured to display the SFTP session logs to help troubleshooting.
Note 1: the SFTP activity uses ~/.ssh/id_dsa instead of ~/.ssh/id_rsa:
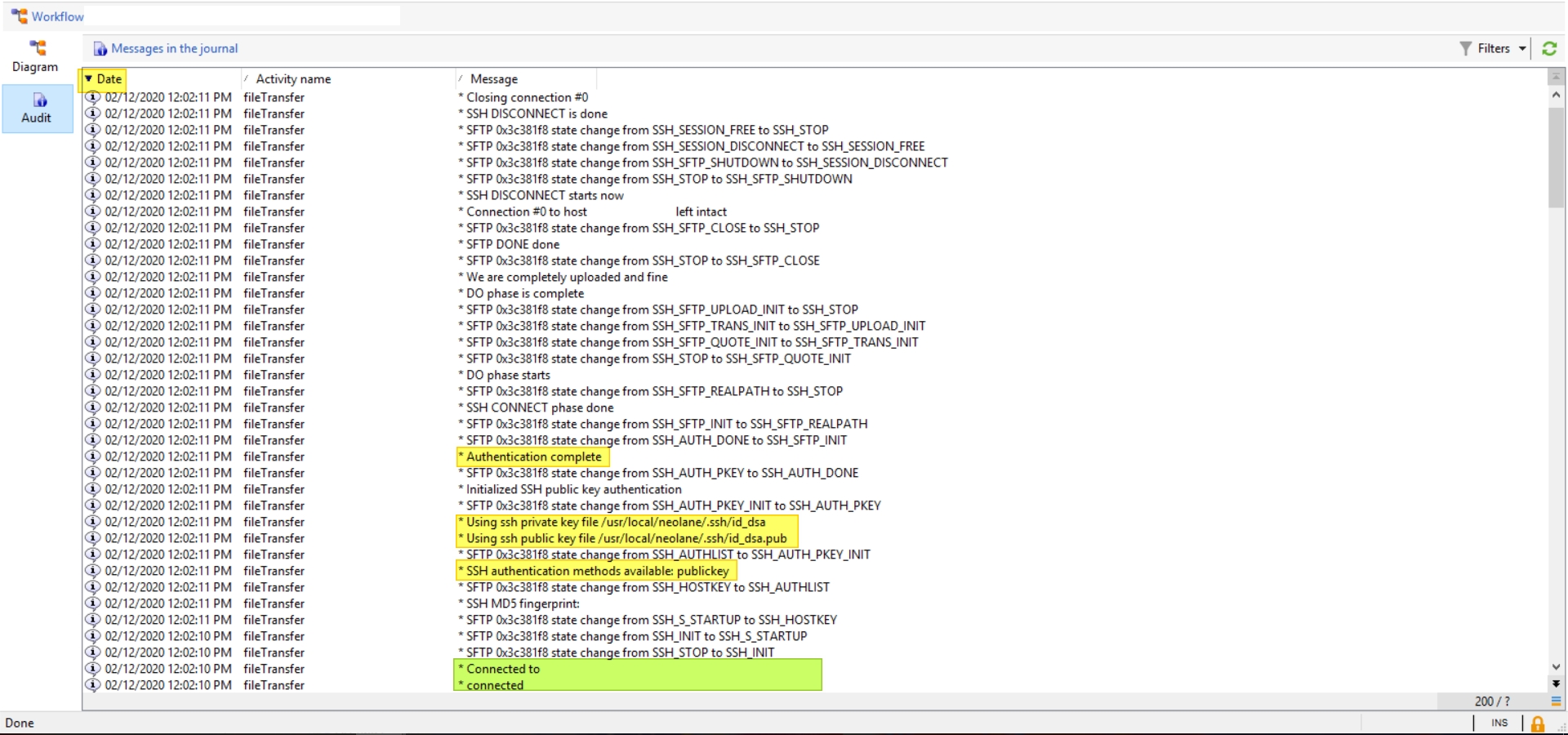
04/13/2021 1:42:48 PM fileTransfer * Using ssh public key file /usr/local/neolane/.ssh/id_dsa.pub
04/13/2021 1:42:48 PM fileTransfer * Using ssh private key file /usr/local/neolane/.ssh/id_dsa
04/13/2021 1:42:48 PM fileTransfer * SSH public key authentication failed: Unable to open public key file
04/13/2021 1:42:48 PM fileTransfer * Authentication failure
04/13/2021 1:42:48 PM fileTransfer * SSH DISCONNECT starts now
04/13/2021 1:42:48 PM fileTransfer * SSH DISCONNECT is done
04/13/2021 1:42:48 PM fileTransfer * Login denied
04/13/2021 1:42:48 PM fileTransfer Login denied
04/13/2021 1:42:48 PM fileTransfer CRL-290002 Download error in cURL
So you might need to copy id_rsa to id_dsa:
loadLibrary('fco:helpers');
sh.exec('cp ~/.ssh/id_rsa ~/.ssh/id_dsa');
sh.exec('cp ~/.ssh/id_rsa.pub ~/.ssh/id_dsa.pub');
sh.exec('ls -alh ~/.ssh/');
Note 2: the green area shows that the IP+port are reachable. It means that:
- The IP exists (public IP)
- The port is open and accept connections
- The firewall installed on this server has accepted us (may be via IP whitelisting)